When accidents happen on the road, it does not matter if you drive a 4×4 truck or a smart car. The same analogy applies to business risks; the size of your business does not matter. The Internet is just like the road allowing businesses of all sizes to reach other markets searching for opportunities, using a vehicle such as a computer or a mobile device. Just as accidents can happen with any car on any road, business risks can arise from any cloud-based application, email, smartphone, or third-party software. Reports suggest theft of digital information has become the most commonly reported fraud, surpassing physical theft. Every business that uses the Internet should foster a culture of shared responsibility for cybersecurity, leading to enhanced business and consumer confidence.
Cybersecurity and data privacy principles must be embedded into decision-making at all levels of the business. It is even more critical for companies such as medical and dental clinics, accounting, and law firms, which should guide all their business decisions to ensure patient and client personal data protection is their core priority. It should be no surprise that the bulk of cybersecurity breaches originate from some form of human error, be it a victim of a phishing email or weak passwords. For these reasons, businesses need to build a cyber-secure culture to protect their own business, clients, and data from growing cybersecurity threats.
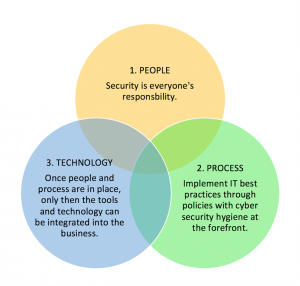
The culture of any business drives people’s decisions when at work, and the human element of cyber awareness is the key to a cyber-secure business. An overall cyber-secure culture starts from the top, leading the way and setting an example for their employees. You cannot have business owners or leaders share their passwords with an office assistant! That is not how you build a cyber-secure culture. I often hear business leaders willing to spend on the shiniest object when it comes to purchasing a security solution in the hopes to cyber-secure their business. Business leaders need to understand cybersecurity because one does not work without the other; it is a combination of People, Process, and Technology.
At the time of writing, COVID-19 continues to spread widely worldwide, disrupting businesses in many ways. This disruption has led to employees shifting to a work-from-home model. Not only does this pose new challenges for companies in supporting their employees. It also puts an even more significant burden on the employees who must quickly adapt to a new way of working from home—and do so safely and securely away from the traditional office. Cybercriminals are taking advantage of people’s heightened levels of concern and genuine fear around COVID-19, trying to spread misinformation leading to fraud and theft of employee and customer information.
Cybersecurity is an evolving and growing business risk and should be taken very seriously. It does not have to be expensive, as long as proper cyber hygiene is integrated into every business decision. A list of top 10 cybersecurity tips for small businesses is always a good start:
1) Raise cyber awareness
Establish basic security practices and policies for employees to handle and protect client information and other personal data.
2) Primary computer and networks hygiene
Install security software to defend against viruses, malware, and other threats. Install software updates as soon as they are available.
3) Secure internet connection
A firewall prevents outsiders from accessing data on a private network. If not using a hardware firewall, make sure the operating system firewall is enabled.
4) Create a mobile device policy
Require employees to password-protect their devices, encrypt data, and install security apps to prevent a data breach.
5) Backup business data
Regularly back up critical business data, ensure backups are either offsite or in the cloud.
6) Physical access to computers
Prevent access or use of computers by unauthorized individuals. Laptops can be a specific target for theft, so lock them up when unattended.
7) Secure Wi-Fi networks
Make sure Wi-Fi is secure, encrypted, and hidden.
8) Payment cards best practices
Isolate payment systems from the computer used to surf the Internet.
9) Limit employee access to data, information, and system
Limit employee access to data. Employees should not be able to install any software without permission.
10) Passwords and authentication
Require employees to use unique passwords and change passwords regularly. Consider implementing multi-factor authentication when available.
(This article first published in Drishti Magazine in March 2021, written by Sunny Jassal.)
About Sunny Jassal, Director, Cybersecurity

Sunny Jassal is on a mission to enable and secure digital transformation. A passionate technologist and trusted leader striving to deliver innovative technology solutions with strong credibility across business and technology groups. A change agent, bringing two decades of progressive on-the-ground experience leading highly technical teams from Enterprise Architecture, Network Operations, Application Development, Cyber Security and Risk Management across various sectors.
Sunny has special interests in Cyber Security and leads by the principle of ‘security by design’. In his current role as Director, Cyber Security at BCIT, Sunny provides leadership and oversight over all aspects of Cyber Security and IT Risk Management; ensuring critical systems and assets are protected and kept secure. Sunny holds a B.Tech in Technology Management from BCIT along with top industry certifications like, Certified Chief Information Security Officer (CCISO), Certified Information Security Manager (CISM), Certified Data Privacy Solutions Engineer (CDPSE) and Systems Security Certified Practitioner (SSCP).
Sunny is an active member of, and participates in, various local, national and international Cyber Security and Risk Management communities. Sunny also serves on number of boards providing strategic leadership and direction to various programs and initiatives.

Cybersecurity is an ever-changing and expanding business issue that must be treated carefully. It does not have to be costly as long as basic cyber hygiene is incorporated into all business decisions. Thank you!